Programmatically filter unusual DNS Requests with Cisco Umbrella APIs
We use the Web in our on a regular basis lives to get work performed, handle our lives, and even socialize. We take this Web utilization as a right lately, however the actuality is that we’re speaking greater than ever on a worldwide scale, instantaneously, and sometimes, with of us we’ve by no means met in-person or with third-party providers we don’t absolutely perceive.
From a cybersecurity perspective, this seems like a variety of DNS site visitors to have to observe, perceive, and examine. And, there are growing causes to just do that. After the main Colonial Pipeline ransomware assault that resulted in a $4.4 million ransom fee in 2021, the TSA issued (and has since, reissued) a safety directive to pipeline utility firms that, partly, requested them to higher perceive their DNS site visitors.
In fact, pipelines should not the one targets of such assaults, that means we want cheap methodologies for figuring out and investigating doubtlessly malicious domains. On this article, we stroll you thru the way you would possibly programmatically acquire visibility into and examine unusual DNS requests utilizing Cisco Umbrella APIs.
Preliminary developer setup
To create this automation, we assume you could have an energetic Cisco Umbrella account with API entry, Python3, and an built-in developer setting (IDE) that helps Python.
When you’re not but an Umbrella person, otherwise you’d merely wish to create a proof-of-concept (POC) round this, you possibly can leverage the always-on Umbrella Safe Web Gateway sandbox by means of Cisco DevNet.
Defining what site visitors is “unusual”
The day earlier than writing this text, Cisco Umbrella processed over 800 billion DNS requests. Because of this persistently huge quantity of site visitors processing and evaluation, Umbrella maintains an updated “Prime 1-Million Domains” checklist as a CSV. This info establishes a baseline of what site visitors is frequent.
We will decide what site visitors coming out of your Umbrella community is unusual by evaluating it to this Prime 1-Million Domains checklist.
To do that, we make an API name utilizing the Umbrella Studies API to retrieve the Prime Locations seen by your Umbrella community prior to now week. The decision returns a listing of domains from most to least frequent, one per row, as a CSV, that we will clear to take away the rank order and non-domains. (For instance, take away the 8 on this row: 8,www.google.com, and take away IP tackle locations as a result of they gained’t match an Umbrella Prime 1-Million area)
We will then write logic that compares the domains seen by your community to Umbrella’s Prime 1-Million and provides any of your domains that aren’t on that checklist to a brand new CSV.
Pattern Code
We’ve written a pattern Python script that can assist you obtain this utilizing your individual DNS site visitors! That script, together with directions for operating it, might be discovered right here.
Investigating unusual domains with Umbrella APIs
When you’ve recognized which domains seen by your community are thought-about much less frequent, you might select to additional examine some—or all—of them utilizing Umbrella Examine.
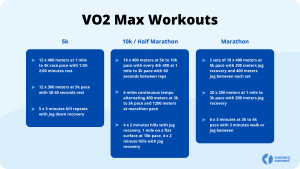
In case you have an Umbrella DNS Safety Benefit or Safe Web Gateway (SIG) package deal, within the Umbrella dashboard, you possibly can navigate to Examine > Sensible Search and seek for the area you’d like to research. You’ll see outcomes that present info wanting one thing like what you see beneath for examplemalwaredomain.com:
 Determine 1: The start of Umbrella Examine outcomes for examplemalwaredomain.com
Determine 1: The start of Umbrella Examine outcomes for examplemalwaredomain.com
The outcomes first present you each the content material and safety classes for the area, offered by Cisco Talos. We will see that this area is assessed as malware and is already on a Malware Block Listing; although, if we wished to, we may discover extra info on this area throughout Talos, Google, or VirusTotal (high proper).
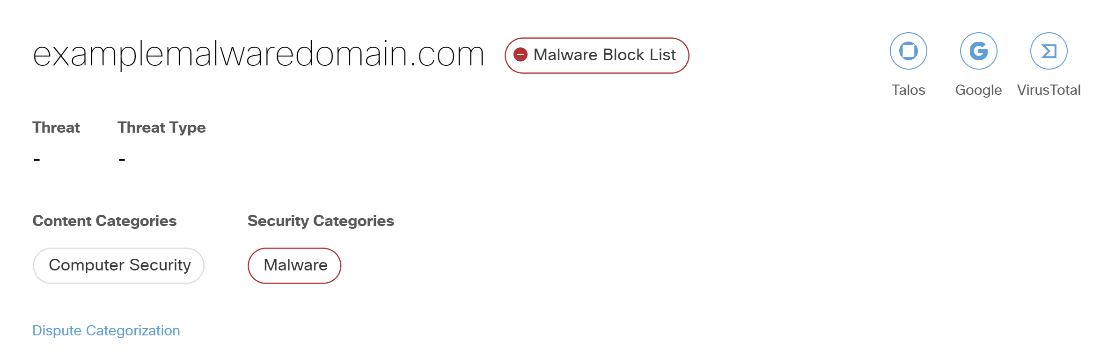
 Determine 2: The chance rating and safety indicators for examplemalwaredomain.com
Determine 2: The chance rating and safety indicators for examplemalwaredomain.com
Scrolling down the outcomes, we subsequent see the chance rating assigned to this area and the safety indicators that went into calculating that rating. On this case, the area is assessed as Excessive Threat, with extra info on the safety indicators used right here.
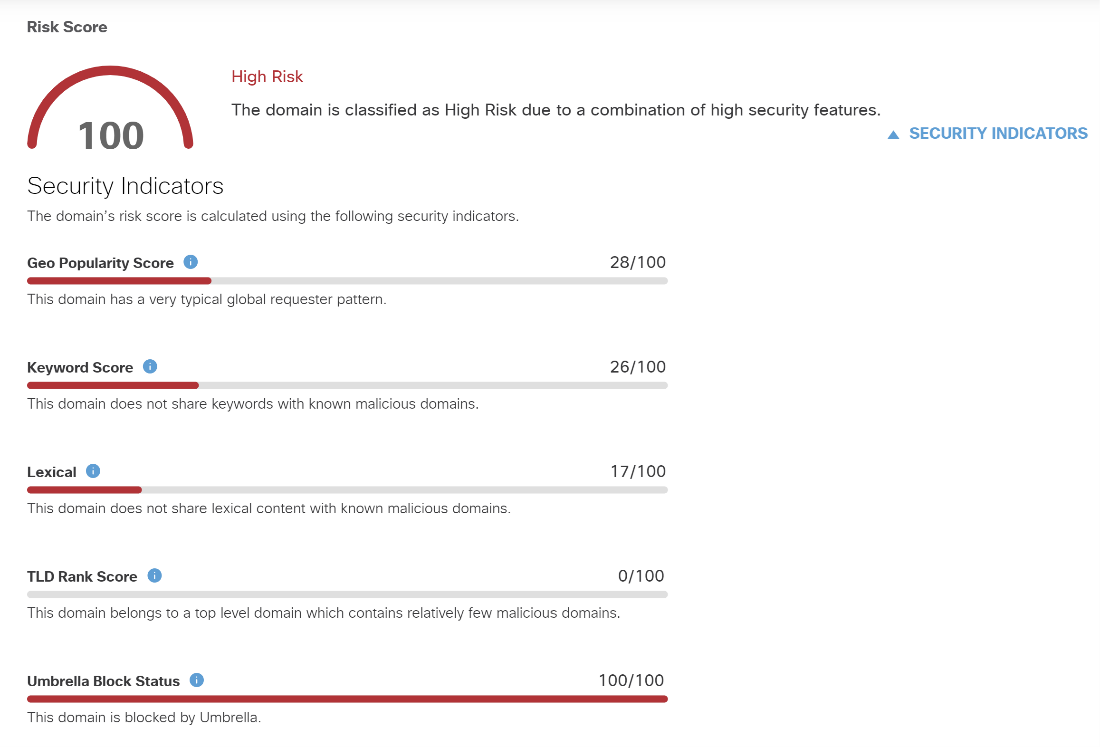
After viewing fundamental info on the area, resembling when it was created and from what nation it originates, in addition to related observables like IP addresses, identify servers, and recordsdata, you’ll discover WHOIS report info on the area (see beneath). You’ll discover that Umbrella Examine means that you can additional examine the related electronic mail tackle and nameservers.
 Determine 3: WHOIS report information for examplemalwaredomain.com
Determine 3: WHOIS report information for examplemalwaredomain.com
Lastly, we will view a worldwide map exhibiting the place DNS requests to examplemalwaredomain.com. Within the instance map beneath, over 95% of DNS requests to this area originate from the US.
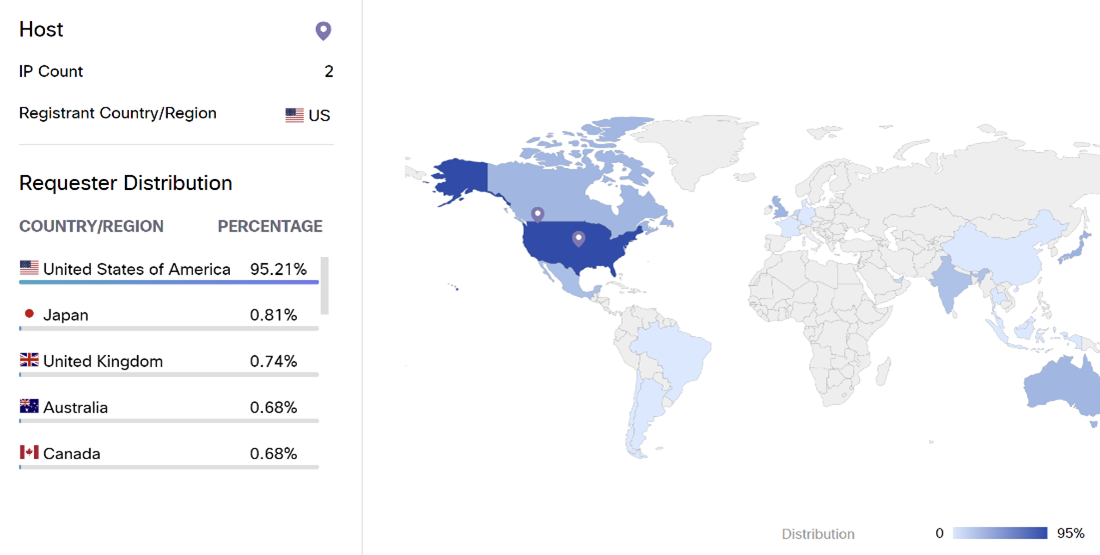 Determine 4: International requestor distribution map for examplemalwaredomain.com
Determine 4: International requestor distribution map for examplemalwaredomain.com
These Umbrella Examine outcomes are additionally accessible as a part of the Umbrella Examine API, that means that the investigation of those unusual domains will also be performed programmatically.
Further alternatives for automation
What are the probabilities for constructing upon the automation we’ve offered within the pattern code?
- Examine – including logic that for every unusual area, an API name is made to the Umbrella Examine endpoint to retrieve information and any risk intel
- Ticketing – you could possibly combine a ticketing system, like Jira, by leveraging its API to create and assign a ticket for every unusual area
- Coverage Modifications – use the Umbrella Locations Listing API to permit or block a number of of the unusual domains
- Reporting – export the unusual domains, and maybe information on them from Umbrella Examine, right into a extra palatable format like PDF. Area information may be enhanced by intel from different safety merchandise, by viewing related gadgets and their relationships with the area utilizing JupiterOne, and/or utilized in a visualization.
- Orchestration – you possibly can orchestration an automation workflow with a number of steps (not all of these steps want be automated) utilizing Cisco XDR. The workflow would possibly embrace all steps your group requires for investigation and incident response.
- Communication – reasonably than save the ensuing CSV of domains regionally, you might select to routinely electronic mail the outcomes to events or submit the outcomes to a messaging platform like WebEx.
Share:
Supply hyperlink